.png?)
When it comes to safeguarding your business communications, choosing the right secure email solution is crucial.
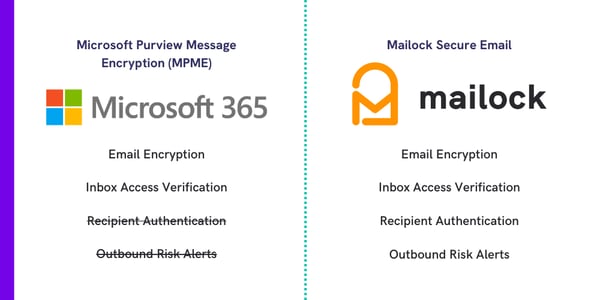
In this review, we look at how Microsoft 365's secure email offering, Microsoft Purview Message Encryption (MPME), compares to Mailock.
MPME, which is typically included in top-tier 365 packages (such as E5) and can also be added to other plans, is an updated version of the legacy Office Message Encryption (OME).
Key features include:
- Military-grade encryption
- Inbox access verification
- Audit trails (limited)
We often receive questions regarding the differences between MPME and Mailock secure email.
So, let's compare the two solutions in terms of their core features for secure communications.
Microsoft 365 Encryption vs Mailock: Key Features
Email Encryption
- Microsoft Purview Message Encryption:
- End-to-end AES-256 encryption
- Encrypted reply option for recipients
- Designed for 'prevention'
- Mailock:
- End-to-end AES-256 encryption
- Encrypted reply option for recipients
- Designed as a security boundary
Security Alerts
- Microsoft Purview Message Encryption:
- No security alerts for users sending confidential data by unsecured email
- Mailock:
- Custom security alerts for users sending confidential data by unsecured email
Recipient Authentication
- Microsoft Purview Message Encryption:
- No recipient authentication
- Mailock:
- Question-and-answer
- SMS code
- Unipass ID
Email Verification
- Microsoft Purview Message Encryption:
- One-time code
- Mailock:
- One-time code
Message Revoke
- Microsoft Purview Message Encryption:
- No message revoke with lower tier plans (e.g., AIP P1)
- Revoke is available for emails sent outside M365 ecosystem (in certain instances)
- Mailock:
- Available with all paid plans (e.g., Pro and Enterprise+)
- Revoke is unilateral regardless of recipient ecosystem
Read Notifications
- Microsoft Purview Message Encryption:
- Read notifications for Outlook recipients (recipient can refuse)
- Mailock:
- Read notifications for recipients regardless of their ecosystem
Message Tracking
- Microsoft Purview Message Encryption:
- Accessible to administrators only, no proof-of-delivery
- Mailock:
- Accessible to senders and administrators, including proof-of-delivery/access
Usage and Limits
- Microsoft Purview Message Encryption:
- Rate limits prevent delivery at high volumes
- Mailock:
- No ceiling on send volume for delivery at scale
Setup/Management
- Microsoft Purview Message Encryption:
- Requires Microsoft specialist familiar with PowerShell
- Mailock:
- Simple deployment, manageable by anyone using admin dashboard
Overview of Microsoft and Mailock Secure Email
What Is Microsoft Purview Message Encryption?
Microsoft Purview Message Encryption is built on M365's Azure Information Protection (AIP) suite of tools for security and compliance.
It uses email encryption and an emailed one-time code to increase the chance of an email reaching the right person without being intercepted.
What Is Mailock Secure Email?
Mailock secure email uses encryption and multi-factor recipient authentication to deliver sensitive information to the right person.
It integrates with Microsoft 365 and Windows Outlook, helping organisations to remain compliant with regulatory guidance, protect valuable data, and deliver sensitive messages at high volumes.
Microsoft Purview Message Encryption (MPME) Reviewed
Microsoft Purview Message Encryption is a preventative barrier to email interception where recipient authentication is not required.
Email Encryption
MPME uses the Azure Information Protection (AIP) suite to encrypt the contents of email messages.
This prevents sensitive message data from being accessed if an email were to be intercepted.
Microsoft has acknowledged a security vulnerability within the Information Protection Suite which makes it unsuitable for use as an enterprise security boundary.
Technically, if someone were to get hold of many secure messages, they could use crypto-analysis to uncover the obscured data.
"The rights management feature is intended as a tool to prevent accidental misuse and is not a security boundary."
Nevertheless, the encryption used by MPME provides enough protection to ward off a majority of email interception attacks.
The additional features that MPME provides (e.g, inbox access verification, message revoke) also strengthen its protection.
Security Alerts
As yet, there is no 'before you send' data loss prevention available with Microsoft Purview Message Encryption.
Encryption must either be applied automatically, to every email, or manually, by users.
There is no way to scan outbound messages for confidential information to present users with warnings or prompts.
Typically, administrators would set up a rule in M365 to encrypt all emails containing the word 'confidential', then rely on users to manually secure sensitive messages that don't meet this criteria.
However, sensitive information could easily fall through the cracks using this method.
Sending an email is so commonplace that employees do not always remember to think twice before hitting 'send'.
Given that sensitive email sent to the wrong person is the top cause of a data breach, providing employees with a safety net that checks the information they are sending by unsecured email is vital.
Companies should invest adequately in data security training for employees using MPME unless they intend to integrate additional tools.
Email Verification
An additional check that a recipient has live access to their email account when they attempt to open a message (with an emailed one-time code) can prevent messages from being opened if they are intercepted.
Email verification is an important preventative measure that helps to eliminate a number of the most common email threats.
This makes it easy for recipients to verify they have access to their inbox on receiving a message, regardless of their email provider.
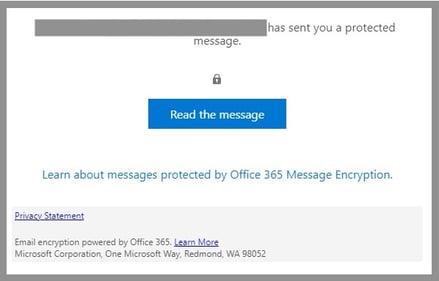
Recipients must click on the link contained within their message, select the verification type, and enter their credentials.
Recipients are not obliged to use email verification, however.
They can also select alternative single sign on (SSO) options to verify that they have a Google or a Microsoft account instead of verifying live access to their email inbox with a code.
In certain other contexts, recipients using a compatible version of Outlook are not required to verify inbox or account access, and messages are automatically decrypted (one factor being whether they have used two-factor authentication at login).
Recipient Authentication
Email verification cannot protect against all risks.
If an unauthorised individual obtains a recipient's account credentials, they can still access all the messages in the inbox.
Email verification may also fail to provide a strong enough record that information has been delivered to the intended recipient, which is key for compliance with certain regulatory guidelines.
For this reason, many secure email solutions offer multi-factor recipient authentication to make sure that only the intended parties can access secure emails, and that evidence of this is recorded.
Microsoft does not currently offer recipient authentication to its 365 Purview Message Encryption users.
| Note: Many recipients of secure emails have two-factor authentication enabled on their email accounts, which helps to ensure that only the intended person can access secure emails. However, this can only be enabled by recipients and is not something over which senders have direct control. |
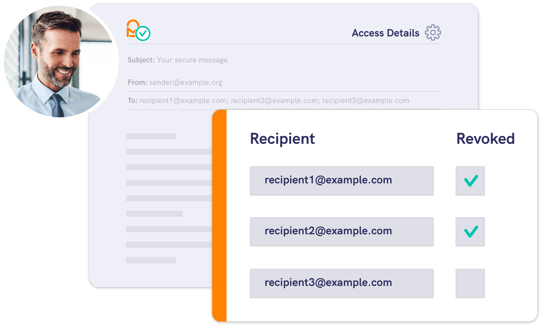
Message Revoke
For emails that have already been sent to the wrong person, MPME provides the ability to revoke secure emails under certain conditions.
This function can be accessed by senders within their Outlook client and by administrators with PowerShell access.
However, it is only available with Azure Information Protection P1 under some M365 plans (e.g., E5).
The revoke function only works if the recipient has received a link-based experience.
If a message has been automatically decrypted, the sender will be unable to revoke access.
This means that secure emails sent to other Microsoft 365 users, most often, cannot be revoked.
Read Notifications
For confirmation that a secure email has reached its destination, senders using MPME can request a read receipt (or notification).
This will prompt the recipient to confirm if they are willing to share that they've accessed the message with the sender upon opening the email.
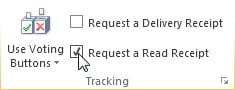
As the recipient chooses whether to allow a read notification to be sent, there are no analytics on open and download rates for secure emails.
This also prevents organisations from gathering proof of delivery for regulatory compliance and in case of litigation.
Message Tracking
For many organisations and their industry regulators, keeping records of sensitive communications is essential.
Microsoft Purview Message Encryption provides a searchable compliance dashboard for sent secure messages including timestamps, revocation details, and expiration periods.
However, this does not include data on recipient access.
For organisations that require proof-of-delivery, message tracking is limited in this capacity as they can only be used as a send record.
The compliance dashboard is only accessible to Microsoft 365 account administrators.
There is no message tracker record available to the individual sender of a secure email.
Usage & Limits
Delivering confidential information to customers at scale is critical for large organisations in regulated sectors such as financial services.
Since MPME is designed as a preventative measure for everyday business email activity, its usage limits do not account for delivery at scale.
Smaller companies will not find rate limits to be an issue, though larger organisations should be aware that there are caps to usage:
- 30 messages per minute
- 10,000 messages per day
If your usage could reach these limits, you should consider other secure email solutions designed for scaled delivery.
Setup & Management
To set up Microsoft Purview Message Encryption for your organisation you will need the help of a Microsoft specialist to configure it in PowerShell.
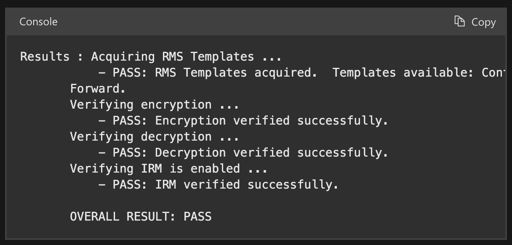
Your Microsoft specialist will have to activate Azure Information Rights Management for your tenancy and set up the rules to apply encryption to custom templates using the message encryption facility.
Mailock Secure Email, Reviewed
Mailock is a powerful solution for the secure exchange of confidential information with customers at any scale.
Email Encryption
Mailock uses military-grade AES-256 end-to-end encryption to protect confidential email data and attachments.
The encryption used by Mailock is designed so that patterns in the encrypted data can't be used to crack it.
Each block of data is injected with an identifier that ties it to the last, making it unique.
"Security is fundamental to the Mailock system, and always comes first.
Our most valued financial organisations use the network to deliver highly sensitive information on a daily basis."
Michael Wakefield, CDO, Beyond Encryption
Mailock's encryption architecture, combined with the authentication challenges it provides, is designed to ensure that only the intended parties can decipher secured messages and attachments.
The end-to-end encryption used by Mailock is also available to recipients of secure emails, who can reply for free.
Security Alerts
How does Mailock prevent users from sending confidential information in an unsecured email?
Organisations can set custom 'trigger words' or use the default set.
When these trigger words are present in an email, users will be alerted to send the email securely.
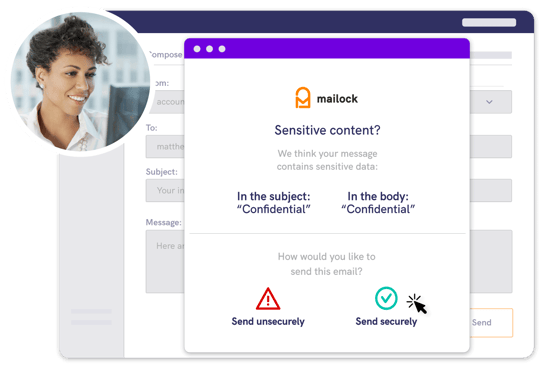
This helps to train employees to think twice before sending an email and prevents confidential information from being leaked.
Administrators can create rules in addition to these user-level prompts to unilaterally force emails to be sent securely when they contain particular keywords or other criteria.
By providing flexible control over data loss prevention, Mailock allows organisations to easily match their protection to their needs.
Email Verification
As with Microsoft's secure email service, Mailock gives its users the option to require a one-time code from recipients of secure emails (sent to their inbox) before they gain access to a message.
This helps to prevent interception by double-checking that recipients have live access to their email accounts.
However, with Mailock, more robust recipient identity authentication methods can also be accommodated.
Recipient Authentication
Authenticating email recipients beyond their inbox access is the only way to ensure sensitive information is delivered to the right people.
Checking that a recipient has instantaneous access to their account when they attempt to open a secure email eliminates a majority of threats.
However, inbox access verification does not stop an unauthorised party who has gained access to a recipient's inbox.
Mailock offers multiple recipient authentication types that go beyond inbox access verification, including:
- SMS: Send a one-time code to your recipient's mobile device.
- Q&A: Ask your recipient a question only they could correctly answer.
- Unipass ID: Allow financial professionals to use their Unipass ID.
Authenticating recipients provides recorded confirmation that a message has been received by the intended party.
Many organisations require such proof-of-delivery for particular types of documentation in order to comply with regulations.
Message Revoke
Access to a Mailock email can always be revoked by the sender.
This can save a small problem from becoming a bigger one by giving a business the power to immediately contain a breach.
Mailock's revoke function stops a recipient from accessing a secure email instantaneously, regardless of their device or email client.
The revoke function is available both to individual senders using Mailock For Outlook and to company administrators via the admin portal.
| Note: Unilateral revoke is a critical feature that helps organisations comply with regulatory guidelines such as the Information Commissioner's Office guidance on misfired emails (emails sent in error to the wrong person). |
Read Notifications
For organisations that need to confirm that sensitive information has been delivered, Mailock also offers read notifications.
Notification settings are accessible within the Outlook add-in and work in every case, regardless of the receiving email client.
Read notifications are useful for anyone wishing to progress a customer along a journey, from sales to customer support, as they can follow up when the customer is most likely to respond.
The ability to track recipient interactions with a message in this way also enables detailed open rate analytics for administrators.
Message Tracking
Need to maintain records of sensitive communications in line with regulatory guidance?
Mailock provides a secure email message tracker, which can be accessed at both user and admin-level.
The message tracker allows users to view timestamps of activity, to revoke messages, and to view all sent secure emails in one place.
Usage & Limits
Mailock is designed to support enterprise organisations that deliver sensitive documents to customers at scale.
For this reason, there is no hard ceiling on the volume of secure emails that can be sent securely.
Mailock is a viable alternative for organisations that deliver a high volume of confidential post and are considering secure email for the cost and carbon savings it affords.
Setup & Management
Setting up Mailock for your organisation is simple.
Depending on your choice of deployment (cloud/on-premise), you will use an installation pack or be guided through the process by a specialist.

The solution can be monitored using Mailock's company admin dashboard - a secure browser-based experience where you can manage your users, email domains, and trigger words.
Microsoft Purview Message Encryption (MPME) vs Mailock Secure Email
Every organisation has different requirements when it comes to choosing a secure email solution that fits, but in a nutshell:
- MPME can prevent email interception
- MPME has no recipient authentication
- MPME is limited in volume/throughput
- MPME setup requires PowerShell familiarity
- Mailock secures sensitive data at any scale
- Mailock offers recipient authentication
- Mailock has no send volume limitation
- Mailock is easy to deploy and manage
FAQs
What Is Microsoft Purview Message Encryption (MPME)?
MPME is a secure email solution within Microsoft 365 that encrypts emails to prevent unauthorised access.
It uses end-to-end AES-256 encryption and an emailed one-time code for recipient verification.
How Does Mailock Differ from Microsoft Purview Message Encryption?
Mailock offers additional security features, such as multi-factor recipient authentication and custom security alerts, whereas MPME lacks recipient authentication and proactive security alerts.
Can I Revoke an Email Sent via Microsoft Purview Message Encryption?
MPME allows email revocation under specific conditions, mainly if the recipient receives a link-based experience.
However, emails sent within the Microsoft 365 ecosystem may not be revocable.
Does Mailock Have a Limit on the Number of Secure Emails I Can Send?
No, Mailock does not impose send volume limitations, making it suitable for organisations that need to send large volumes of secure emails.
Which Secure Email Solution Is Easier to Set Up and Manage?
Mailock is easier to deploy and manage through its user-friendly admin dashboard, while MPME requires PowerShell expertise for setup and configuration.
Reviewed by
Sabrina McClune, 18.06.24
Sam Kendall, 18.06.24
|
Originally posted on 20 01 23
Last updated on July 17, 2025 Posted by: Sabrina McClune Sabrina McClune is a Women in Tech Excellence 2022 finalist who writes extensively on cybersecurity, digital transformation, data protection, and digital identity. With a postgraduate degree in Digital Marketing (Distinction) and a First-Class Honours degree in English, she combines a strong academic foundation with professional expertise. At Beyond Encryption, Sabrina develops research-led content that supports financial and technology sectors navigating the complexities of the digital age. |
Email Series
Subscribe to
Subscribe to Privacy Decoded, our monthly email briefing about privacy, digital trust, and the forces shaping our online world.
 Sabrina McClune
Sabrina McClune